The nightmare of cages and the ferment of contradictions
For the nations collocated (geographically and culturally) in the Western regions of world, August is notoriously a month in which holiday thoughts – in the reality of their transformation, namely either in vacation or frustration – can promote ambiguous feelings that, however, become source of distraction. At moment, we don’t know much about the reason behind temporary downtime of all Google services, but that kind of distraction could explain the fall of one of the main pillar of internet. (Somebody jokingly ties the failure with the fresh decision made by Google to eliminate the possibility for its workers to dedicate part of their job time for projects outside their own specific tasks).
 The blackout lasted 11 minutes (In Europe from 1:37 to 1:48 AM). A such incident didn’t occur since many years but now for internet Google has a much heavier role. To be clear, for some analysts internet global traffic dropped of 40%! Indeed, a big event. “As users, we confide very much on Google ” was a very common comme
The blackout lasted 11 minutes (In Europe from 1:37 to 1:48 AM). A such incident didn’t occur since many years but now for internet Google has a much heavier role. To be clear, for some analysts internet global traffic dropped of 40%! Indeed, a big event. “As users, we confide very much on Google ” was a very common comme nt. However, much of what we use on the Net is structured (fused) on architectures and mechanisms running on computer and networks that are, at the same time, distributed and concentrated (logically but, even more often, physically) in specific service centers managed by few players. The result is that applications/companies become lively parts – relevant and inextricable ones – of internet.
nt. However, much of what we use on the Net is structured (fused) on architectures and mechanisms running on computer and networks that are, at the same time, distributed and concentrated (logically but, even more often, physically) in specific service centers managed by few players. The result is that applications/companies become lively parts – relevant and inextricable ones – of internet.
We can show this compenetration through an another important internet player; among other things Amazon is well-known to be a former supporter and now leader of public cloud computing architecture. In effect, many new internet companies have built their services on its infrastructures, reason for which any Amazon’s failures become a “breaking news”. (In August the same company had an incident that produced a partial stop in some “available Zones”, spreading the effects – to cite only the most famous companies – on Instagram, Vine and Netflix.)
 Famous for its virtual stores, Amazon offers also a wide range of elementary “infrastructural” services that people and companies can utilize to build and manage businesses based on ICT resources. To support these services, Amazon has implemented a network backbone to carry IP traffic accross US, Brazil, Europe, Japan, Singapore and Australia, and linking its own Data Centers full of computers and storage systems. The global infrastructure of cloud computing, storage and networks are organized in 9 “regions”, and each region runs as “data center hub” delivering its own services.
Famous for its virtual stores, Amazon offers also a wide range of elementary “infrastructural” services that people and companies can utilize to build and manage businesses based on ICT resources. To support these services, Amazon has implemented a network backbone to carry IP traffic accross US, Brazil, Europe, Japan, Singapore and Australia, and linking its own Data Centers full of computers and storage systems. The global infrastructure of cloud computing, storage and networks are organized in 9 “regions”, and each region runs as “data center hub” delivering its own services.  Every region has at least an alternative “Availability Zone”, namely it can replicate the services in other location to avoid the “single-point of failure” – each alternative location is diversificated in terms of network links, power supply, sismic zone, etc.
Every region has at least an alternative “Availability Zone”, namely it can replicate the services in other location to avoid the “single-point of failure” – each alternative location is diversificated in terms of network links, power supply, sismic zone, etc.
The structure has a further level of extension consisting in an international network linking 35 “edge locations” in which Amazon has installed app lication servers and storage for data caching in order to replicate (locally) the centralized services for its own end-users. As matter of facts, it obtains both better performance and traffic reducing (on its network backbone, but also on the global internet).
lication servers and storage for data caching in order to replicate (locally) the centralized services for its own end-users. As matter of facts, it obtains both better performance and traffic reducing (on its network backbone, but also on the global internet).
In effect, the ways in which ISP networks link themselves in the Net have changed deeply in the last 15 years. The progressive  deregulation of tlc sectors and the need to have effective and diffuse internet services have pushed toward a simplification of the interconnection levels among the different ISPs (tie1, tier2, …), favoring the rise of national and neutral telco hotels (Internet Exchange Points), places managed by third parties in which network operators can directly interconnected each others. (On the other end, even local ISPs can offer co-location services to host application server and storage systems of other companies).
deregulation of tlc sectors and the need to have effective and diffuse internet services have pushed toward a simplification of the interconnection levels among the different ISPs (tie1, tier2, …), favoring the rise of national and neutral telco hotels (Internet Exchange Points), places managed by third parties in which network operators can directly interconnected each others. (On the other end, even local ISPs can offer co-location services to host application server and storage systems of other companies).
 At the moment, the regional IXPs are over 350 across the entire globe, often sponsored by national authority to guarantee the internet presence of own countries, a way to counterbalance the logic of ROI (Return Of Investment) condemning peripheral and poor nations.
At the moment, the regional IXPs are over 350 across the entire globe, often sponsored by national authority to guarantee the internet presence of own countries, a way to counterbalance the logic of ROI (Return Of Investment) condemning peripheral and poor nations.  Many IXPs, about 20, host more of 100 network providers that develop a growing network traffic comparable in terms of volume to that of big network provider as AT&T or Deutsche Telekom – it is the case of AMS-IX in Amsterdam or DE-CIX in Frankfurt.
Many IXPs, about 20, host more of 100 network providers that develop a growing network traffic comparable in terms of volume to that of big network provider as AT&T or Deutsche Telekom – it is the case of AMS-IX in Amsterdam or DE-CIX in Frankfurt.
 Of course, given the availability and the capacity to find and manage the right solutions – depending on the own development strategy and economic constraints – global operators as Google, Facebook, Microsoft, Yahoo can change and adapt dynamically their own infrastructures deciding flexibly whether they have to rent rooms and networks or implement them independently.
Of course, given the availability and the capacity to find and manage the right solutions – depending on the own development strategy and economic constraints – global operators as Google, Facebook, Microsoft, Yahoo can change and adapt dynamically their own infrastructures deciding flexibly whether they have to rent rooms and networks or implement them independently.
If this is a vision that underlines the ability to play, adapt and rise “in scale” counting on the “mastering” of networking, we must synthetically recall what happens in the software and computing R&D area to truly understand the skill of governance needed to a such infrastructures. In these last decades – thanks to what has been developed on and through internet – industries of microchip, universities and ICT companies have pollinated themselves, finding new paths to properly manage the scale of demand. Companies as Google, Twitter, Facebook, that manage millions of computers and billions of billion of MB of mass storage (peta, exa, zetta, …) have developed “in-house” software to govern the multitude of processors and the huge amount of data in structures more simplified that permit to treat a Data Center as a “unique” computer and a “unique” Data Base on which load and run “transversely” the job processes generated by end-user requests.
 (Rather than run separate software systems on separate server clusters, Google can run everything on one cluster — thanks to Borg and its successor, Omega. Illustration: Ross Patton/ Credit:Wired)
(Rather than run separate software systems on separate server clusters, Google can run everything on one cluster — thanks to Borg and its successor, Omega. Illustration: Ross Patton/ Credit:Wired)
Briefly, even the more sophisticated techniques such as the hardware and software virtualization – nonetheless effective in order to orchestrate the hardware base, and already available in the large market – become ineffective on a such scale.
“There are other ways of doing this. You could use what’s known as server virtualization. But virtualization provides an extra layer of complexity you may not need, and in cutting this out, Wilkes says, Google can reduce the size of its infrastructure by a few percent. At Google’s size, that amounts to an entire facility. ‘It’s another data center we can not build,’ Wilkes says. ‘A few percent here, a few percent there, and all of the sudden, you’re talking about huge amounts of money.’ Google has a software to manage the server clusters named Omega, but also Facebook, Twitter, Amazon, etc. have developed “in-house” similar secret weapons as Mesos, Aurora, Corona …
Un-balancing
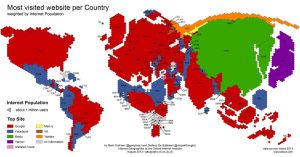 The Oxfors Internet Institute has just published a visual map that shows immediately the product of these efforts in terms of service popularity in the different areas of world. Among the evident consequences of this kind of service architecture, there is the fact that dwellers of Net are citizens of a land technologically governed in an unbalanced way, namely the field of action is delimited and traced by a small and peculiar set of companies. The story seems well-defined: commenting the fresh acquisition of Nokia by Microsoft, many analysts underlined how Europe lost even its last high-tech protagonist while the situation is not good in the ICT sector. “With digital revolution and internet, Europe is entrapped between the US business vitality – capable to invent a global leader every 10 years – and the industrial competition of Asian enterprises. The result is that among the ranking of the first 10 well-capitalized companies of high-tech sector, excluding tlc operators, 9 companies are American and 1 (Samsung) is Asian” (Le Monde). How to counterbalance and distribute the weight remains (if possible) a daunting task involving huge efforts and investments – economic, cultural and political ones. Waiting more robust engagements, we could work on the wake of a more general governance, addressing the internal contradictions of a “system” that, however so consolidated, has a deeply cultural nature.
The Oxfors Internet Institute has just published a visual map that shows immediately the product of these efforts in terms of service popularity in the different areas of world. Among the evident consequences of this kind of service architecture, there is the fact that dwellers of Net are citizens of a land technologically governed in an unbalanced way, namely the field of action is delimited and traced by a small and peculiar set of companies. The story seems well-defined: commenting the fresh acquisition of Nokia by Microsoft, many analysts underlined how Europe lost even its last high-tech protagonist while the situation is not good in the ICT sector. “With digital revolution and internet, Europe is entrapped between the US business vitality – capable to invent a global leader every 10 years – and the industrial competition of Asian enterprises. The result is that among the ranking of the first 10 well-capitalized companies of high-tech sector, excluding tlc operators, 9 companies are American and 1 (Samsung) is Asian” (Le Monde). How to counterbalance and distribute the weight remains (if possible) a daunting task involving huge efforts and investments – economic, cultural and political ones. Waiting more robust engagements, we could work on the wake of a more general governance, addressing the internal contradictions of a “system” that, however so consolidated, has a deeply cultural nature.
We must make a premise: the ability of these enterprises to offer and, above all, manage these technological wonders is undoubtedly a huge merit for the possibilities and activities open to the entire humanity, that appreciates (and rightly desires) their products. Yet, that configuration becomes dangerous also for the same winning companies. Getting their success from a global market and often from user well willing – almost all services insist on business model based on advertising – they are demonstrating, lacking legal constraints based on an international jurisdiction, to be subjected to the national, sinister interests, with the result to put at risk their “business place”. The release of documents and interviews regarding the mega spying project named PRISM, organized by US agency NSA, are underling this fragility. If who lives in the periphery can quietly affirm that “everybody browses internet is always under US jurisdiction” (Il Manifesto), from the centre of empire the Pew Research Center’s Internet Project and the Carnegie Mellon University find that “90% of internet users” have taken or are thinking to adopt some kind of measure to avoid to be controlled during their online activities.
Some US communication companies specialized in security, Lavabit and Silent Circle, have ended their activities because privacy can’t be guaranteed. Microsoft and Google, eventually allied, have sued US administration for their impediment to show the original NSA requests and, they affirm, the narrowness of returned information.
Unfortunately, once the field is mined, the suspect to use or have at home equipments or software potentially “dangerous” (and with some “back doors” open) is a misgiving similar to that blamed on ICT products sold by China, and it is beginning to echo also in the mind of friendly nations (see Germany) (Zeit Online) – US administration and Congress discourage the use of Chinese Technology in the vital sectors of tlc services after the complaints to be object to international hacking actions (BusinessWeek)!
But “internal” contradictions go beyond business. Indeed, some concerns rise nearby given the real shrinkage of space for new enterprises and the very way to create products in the web. For example, everybody starts with free services to attract users, hoping to sell advertising, but overcrowding and competition are very high while famous players already have relevant positions, some ones alone 30-50% of market share, considering the fruition from PC or mobile device. While the typical experience of browsing happens knowing to pay in terms of personal data kept and analyzed in some remote data warehouse, people go ahead trying to skip visual traps that want to attract them in some infernal click.
 On the other side, in the vital function of searching there are real dominators that explore new ways to show data in which it is difficult to distinguish organic results from sponsored ones or other related proposals (the illustrations show organic results in the red rectangle and the percentages of screen dedicated to the “useful” screen spaces. Credit/Aaron Harris di Tutorspree). Of course, things go worse on the small screen of mobile devices…
On the other side, in the vital function of searching there are real dominators that explore new ways to show data in which it is difficult to distinguish organic results from sponsored ones or other related proposals (the illustrations show organic results in the red rectangle and the percentages of screen dedicated to the “useful” screen spaces. Credit/Aaron Harris di Tutorspree). Of course, things go worse on the small screen of mobile devices…
In the name of a creativity betrayed in the research of an excellent aesthetic aiming to establish correct and satisfied relationships with users, the US designer Matthew Butterick protests energetically against the drifts produced from these strategies, facilitated by some web players even with developments that by-passing the slower processes of web technologies standardization.
“Think about Facebook and its mission statement. Facebook’s mission—I hope you know—is “to make the world more open and connected.” Did you ever wonder what Facebook means by “open and connected”? Well, they’ve told us.. They mean “bigger, more media-rich ad formats.” They also mean “really rich things like big pictures.” I don’t know about you, but when I think about “open and connected,” I don’t think about really big ads. But that’s what they mean”. (The bomb in the garden).
Sue Gadner is the executive director of Wikimedia Foundation, the non-profit organization supporting Wikipedia. In a talk at the 2013 MIT-Knight Civic Media Conference in Boston, she came back much warried on argument.
“The internet is evolving into a private-sector space that is primarily accountable to corporate shareholders rather than citizens. It’s constantly trying to sell you stuff. It does whatever it wants with your personal information. And as it begins to be regulated or to regulate itself, it often happens in a clumsy and harmful way, hurting the internet’s ability to function for the benefit of the public.”
Wikipedia is the 5th top web site but the only non-profit among the first 25th top ones. Although the success and the wonder elicits on people, it remains an exception that confirms the rule. On the other side, its non-profit nature generates an other kind of wonder.
“In Silicon Valley, people often find that astonishing—they ask me why Jimmy Wales “left so much money on the table,” and whether he regrets doing it. (Answer: no.) Sometimes people ask me why we don’t just put ads on the site, and whether we are against advertising, against for-profit companies, against capitalism. We say no. Our view is that the internet should have balance, much like the offline world. A city has restaurants and shops and banks as well as schools and libraries and parks. Wikipedia is like a park. It’s a public space, accessible and used by everybody.
But where are the other parks? … But we should be honest: we are not gaining ground. Our schools, our libraries, our parks—they are very, very small and they may or may not sustain…. We certainly have no information-sharing participatory Garden of Eden, the promise of the internet that we all originally believed in. Though we are not lost, we are losing.” (Quartz).
 Quinn Norton is a US journalist expert of hacking, technology and internet – among other things, she had the opportunities to live for 3 years beside of the beloved Aaron Swartz, the geek and hacker committed suicide (January 2013) after to be heavily accused and sued by Federal prosecutors for copyright infringement to have downloaded and diffused magazine articles owned by MIT. Recently, she published an article dedicated to a story of an other famous geek, the soldier Bradley Manning, whose strong and (at the same time) fragile person still divides American people. As ICT analyst enrolled in Iraq in 2009, he is both a hero and a betrayer to have been the source of top-secret documents delivered to Jiulian Assange/Wikileaks ((Illustration: Bradley Manning Credit/Wikipedia).
Quinn Norton is a US journalist expert of hacking, technology and internet – among other things, she had the opportunities to live for 3 years beside of the beloved Aaron Swartz, the geek and hacker committed suicide (January 2013) after to be heavily accused and sued by Federal prosecutors for copyright infringement to have downloaded and diffused magazine articles owned by MIT. Recently, she published an article dedicated to a story of an other famous geek, the soldier Bradley Manning, whose strong and (at the same time) fragile person still divides American people. As ICT analyst enrolled in Iraq in 2009, he is both a hero and a betrayer to have been the source of top-secret documents delivered to Jiulian Assange/Wikileaks ((Illustration: Bradley Manning Credit/Wikipedia).
It is worth to recall her considerations to describe the tensions animating the “empire” and these (yet) new lands.
“To talk meaningfully about Manning, we are left talking about the forces that have acted on him. We have to talk about America, the Internet, and ultimately ourselves.
To one side, Manning’s release of classified material into the public purview is a declaration of the people’s right to know, and an angry comment on how the world is run behind closed doors. To the other, it represents a force threatening to undermine the system that holds America together.
If you see America as a place within borders, a bureaucratic and imperial government that acts on behalf of its 350 million people, if you see America as its edifices, its mandarins, the careful and massive institutions that have built our cities and vast physical culture, the harsh treatment of Manning for defying that institution makes sense, even if it was, at times, brutal.
But if you see America as an idea, and a revolutionary one in its day, that not only could a person decide her fate but that the body of people could act together as a great leader might lead — and that this is a better way to be — Manning didn’t betray that America.
The second America doesn’t have that name anymore. It morphed and grew just as the first, promulgated for a moment from the east side of the mid-North American continent, but going on to become a sense of democracy, the rights of man. It merged with the other spirits born of the Enlightenment and became the force behind science, technology, free speech, and populist will.
Then the ideas of self-determination and the freedom to know blossomed as they never had before in the dying days of the 20th century. The second America became a strange and amorphous transnational creature. It became networked. Both Americas were so successful they are at this point slightly startled to find they have to share the world with the other. All the while, the law, a poor third player in this drama, has tried to straddle the two like a man trying to stand on two battleships while they drift apart.” (The Medium).
Eventually, I would end noticing that every day – in the speedy progress of events – we can register interesting insertions into the queue of the critical activists. Against the insensitive behaviours toward the human patrimony living the internet, and against the consequent free-ride actions, some relevant voices begin to rise from the same riverbed of internet technologists. Strong words those expressed by security expert Bruce Schneier, who wittily underlines how now people feel themselves as a “betrayed spouse” that can’t grant anything, for instance, the trust about a neutral approach by entities of standardization to define and develop network technologies aiming only to solutions based on efficient techniques and common interests (threatpost). He appreciates the “whistleblowers” and speaks in the name of a “moral duty” that contrasts the undermining of “the fundamental social contract” on which the creation and development of internet is based.
“To the engineers, I say this: we built the internet, and some of us have helped to subvert it. Now, those of us who love liberty have to fix it.” (The Guardian).
References
“Bruce Schneier on the NSA, Cryptography and Trust“, threatpost.com, 11/9/2013.
“Bundesbehörden sehen Risiken beim Einsatz von Windows 8”, Zeit Online, 29/8/2013.
“How Google is Killing Organic Search“, TutorSpree Blog, 1/7/2013.
“How we are losing the war for a free and open internet”, Quartz, 1/7/2013.
“Is Huawei Giving Up on the U.S.? Pretty Much”, Business Week, 24/4/2013.
“Internet, intercettazioni in salsa tutta americana”, Il Manifesto, 3/9/2013, p. 11.
“La chute de Nokia confirme le déclin de la high-tech européenne”, Le Monde, 5/9/2013, p. 5
“Microsoft, Google team up to sue federal government over NSA spying”, Yahoo! News, 30/8/2013.
Norton, Q., 2013, “Bradley Manning and the Two Americas“, The Medium, 21/8.
Pew Research Center’s Internet Project, Anonymity, Privacy, and Security Online, 5/9/2013.
“Return of the Borg: How Twitter Rebuilt Google’s Secret Weapon“, Wired, 3/2013.
“Silent Circle Shuts Down Silent Mail, Marking Yet Another Encrypted Email Service To Bite The Dust”, The Huffington Post, 9/8/2013.
“The Bomb in the garden“, Talk given by Matthew Butterick at TYPO San Francisco, 11 April 2013.
“The US government has betrayed the internet. We need to take it back“, The Guardian, 6/9/2013.
“The N.S.A. and Its Targets: Lavabit Shuts Down”, The New Yorker, 8/8/2013.